What Are The Don’ts Of Control Room Design?
- By john.pbtm
- •
- 01 May, 2017
- •
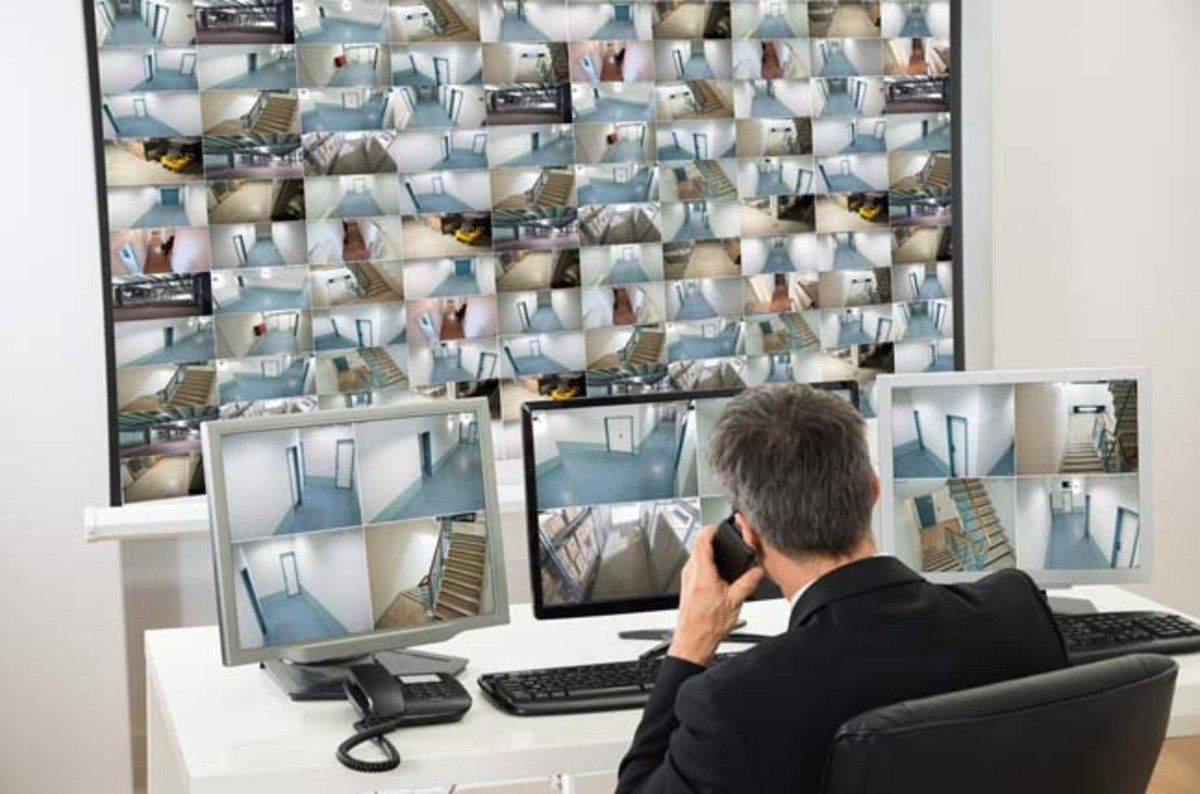
Terrorism, robbery and many other accidents like this are the main concerns due to which we consider security as an important aspect of this era. The design of the control room from where the security matters are watched also holds the key to better protection from such accidents.
It is important for an organization to give importance to the design of the control room. If it is designed well, according to the defined modern norms then the chances to remain safe from many accidents increases a great deal. Thus, we can say that CCTV control room design holds a vital key in all the security matter.
Don’ts of Control Room Design:
Poor and Open Cabling:
When a control room is designed the cables should not be left open and all of them must be connected and joined properly. They should be covered in a duct so that they don’t destroy the physical look of the room. The poor and open cabling can often lead to different problems.
Unauthorized Access:
No Passwords on Systems:
The different systems which are present in the control room should contain the passwords. The password protection will keep the systems from any suspicious activity. So don’t ignore it either.
No Documentation:
Using Second Hand Equipment:
Your control room holds the key to better results regarding the security of your building. That’s why, make sure you use the new and genuine equipment in it. Use of the second hand tools and equipment should strictly be avoided.
Conclusion:
Mentioned above are the Don'ts of the CCTV control room design. One should never forget to make sure that all these matters are kept in mind and avoided while setting up a control room. If all these Don'ts will be kept in mind and avoided, the later result would definitely be worthwhile.



In this advanced era, we can never deny the usefulness and the need of the information security consulting firm. They really are the right ones to be approached, to safeguard a business’s information security matters. For a better security hygiene, you must take this advice seriously, certainly it will pay you off a great deal.